Tag: network
-
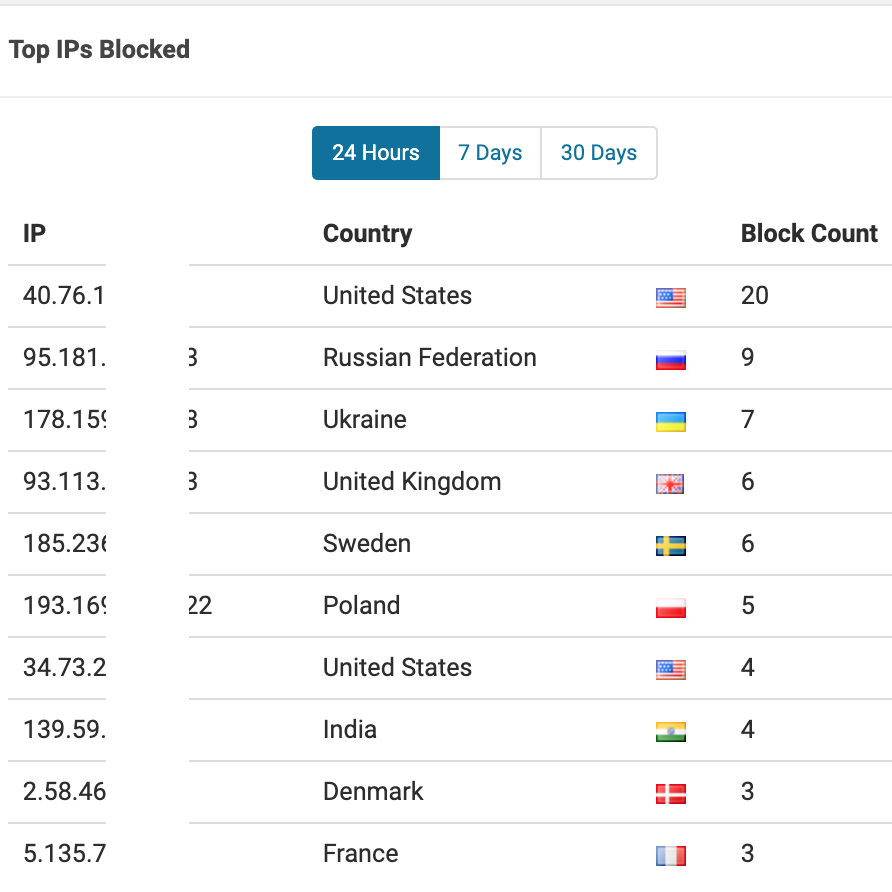
carbonic.live is under attack by automata
by Lyno Carbonic on Sunday, December 27, 2020, at 7 AM With a heavy sigh I begin this post. The truth in a nutshell is that carbonic.live has been hanging out there for quite some time on the internet. Exposed to coordinated attacks by swarms of automata. I am still letting that reality sink in.…
